Hi, I'm Merroun Lahcen from DevSecure — we specialize in uncovering hidden vulnerabilities that pose real-world risks to modern web applications.
All vulnerabilities shared in these write-ups are fully redacted — any company names, domains, or sensitive details are replaced with placeholders such as company.com. Each finding was responsibly disclosed through the Intigriti platform and has been verified and resolved by the affected vendor.
Every post represents our commitment to ethical hacking, responsible disclosure, and continuous learning — helping organizations strengthen their defenses while contributing to a safer global cybersecurity ecosystem.
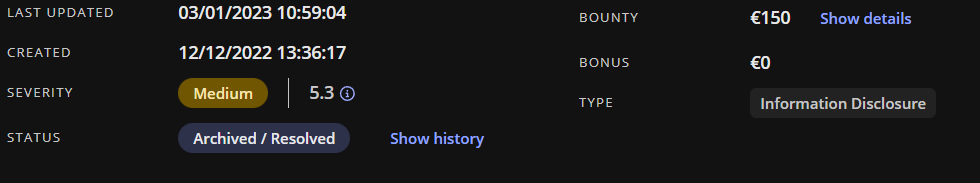
in this article i will share how easy some bounties could be
POC
this document should not be public in the internet i find it using google
in this document ther is a lot of information about this user including digital signature
https://www.info.company.com/pathtopdfhere.pdf
you can find this document in google searching
site:info.company.com filetype:pdf