Hi, I'm Merroun Lahcen from DevSecure — we specialize in uncovering hidden vulnerabilities that pose real-world risks to modern web applications.
All vulnerabilities shared in these write-ups are fully redacted — any company names, domains, or sensitive details are replaced with placeholders such as company.com. Each finding was responsibly disclosed through the Intigriti platform and has been verified and resolved by the affected vendor.
Every post represents our commitment to ethical hacking, responsible disclosure, and continuous learning — helping organizations strengthen their defenses while contributing to a safer global cybersecurity ecosystem.
External Guest without permission Can View pinned-collections Lists
1/ login with owner user role click on invite user chose external ( Guest )
from there you can read
Guests can only read, upload, and download documents in projects which they are invited to.
2/ get your jwt token for the invited guest user with post request include guest credentials to
https://api.company.com/auth/token
2/ you can view all pinned-collections in this company from this endpoint
with GET request
GET /api/pinned-collections
make sure you have some pinned collections in the company
Impact
information disclosure.
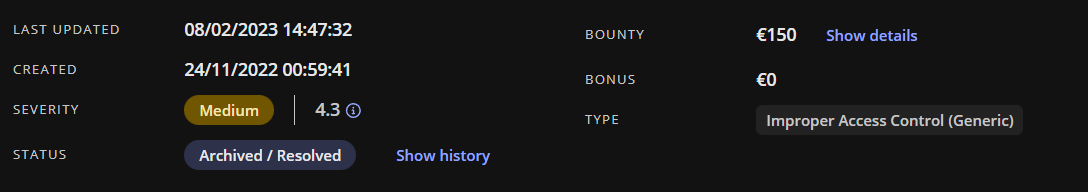
Platform : Intigriti
Timeline :
Reported: 24/11/2022
Triaged: 25/11/2022
Accepted & paid: 28/11/2022
Bounty: €150